Hi,
I followed this set of tutorials “gain-flexibility-and-increase-privacy-with-wireguard-vpn” and now have Wireguard running on my Odroid single board computer at home (running on DietPi).
This little server has two purposes; an instance of Nextcloud which I would like to access from WAN-side securely, and it also runs Pihole. I access Nextcloud at mydomain.com/nextcloud/
On my Mac laptop I have two ‘locations’ for my network settings - pi-hole and no-pi-hole - for use on my lan and from outside my lan.
The WireGuard VPN that I set up only allows me to use it when I am on the no-pi-hole settings, as I didn’t incorporate Pihole into the configuration as I don’t know how to.
I’d like to get this up and running soon as Semester 2 starts soon and I’d like my reference docs and notes with me. I’d also like ad-blocking from outside the lan too.
I found this but have yet to implement anything from it.
I’d really love some help in getting this final piece of the puzzle crossed off. Previously I just relied upon https certificates and fail2ban for securing Nextcloud.
To reiterate:
-
When I have ‘normal DNS settings’ I have internet access through my Wireguard tunnel but no access to mydomain.com
-
My public IP doesn’t seem to change regardless of whether the WireGuard VPN is activated or not
-
No internet access if I use my Pihole ip as the DNS settings
Bit of an update:
Seems I have no internet access if I use the network profile for my Pihole server. DNS queries are going nowhere.
I stopped the Wireguard server with sudo systemctl stop wg-quick@wg0 and the result is the same.
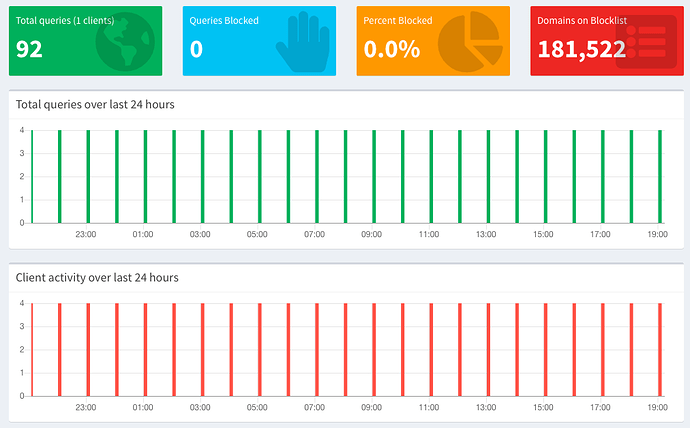
Pihole screenshot - something is weird. Each bar appears to be ten minutes in the hour.
This seems different behaviour from last night and I don’t know what has changed. If I can’t get this sorted within a week I’ll have to revert to my previous set up.
Hoping someone can help. I’m in Australia so time differences will be awkward.
Hey @Capt_Barnacles,
Thanks for your post. Just letting you know that I am working on a configuring a similar set up but I ran into some issues in trying to replicate the problem you were having.
I’ll have to resolve this issue first before I can replicate your set up, but in the mean time can you post what you have for your server config and your client config?
Make sure to anonymize your keys and IP addresses before posting.
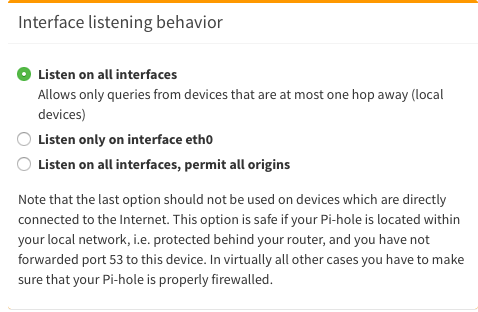
My gut feeling is that when you install PiHole, you might have to set the server to listen on your Wireguard Interface. Similar to this: https://medium.com/@aveek/setting-up-pihole-wireguard-vpn-server-and-client-ubuntu-server-fc88f3f38a0a
Thanks Jay,
The wg0.conf is
[Interface]
Address = 10.0.0.1/24
SaveConfig = true
PostUp = iptables -A FORWARD -i %i -j ACCEPT; iptables -t nat -A POSTROUTING -o eth0 -j MASQUERADE
PostDown = iptables -D FORWARD -i %i -j ACCEPT; iptables -t nat -D POSTROUTING -o eth0 -j MASQUERADE
ListenPort = 51820
PrivateKey = **************************************************
[Peer]
PublicKey = IV+gSeNUmr4Mjmvika2Sw1vQiu9uoHWKXT5BiMwfvgA=
AllowedIPs = 10.0.0.3/32
And the client conf is
[Interface]
PrivateKey = ********************************************
Address = 10.0.0.3/24
DNS = 1.1.1.1,1.0.0.1
[Peer]
PublicKey = nDE4g8wt8MvPWrQ4tLVr2Mqdtxmg1fh9N1cat9ZH3nM=
AllowedIPs = 0.0.0.0/0
Endpoint = 111.222.33.444:51820
I’ll read over that other document and see if I can find the solution.
OK, bit of an update;
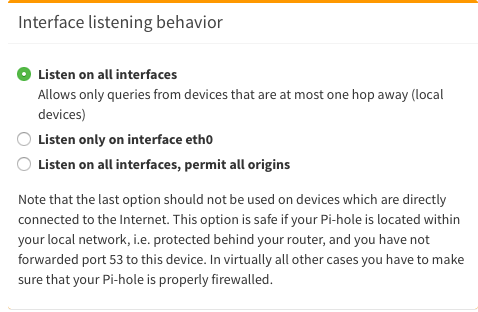
I changed a setting in Pihole’s settings to ‘listen on all interfaces’. It was previously on the second option in the screenshot below.
Running sudo wg shows
peer: ***************************************
endpoint: 192.168.20.1:54836
allowed ips: 10.0.0.3/32
latest handshake: 8 seconds ago
transfer: 8.73 MiB received, 10.16 MiB sent
Anyway, with either of my two network locations selected (pi-hole and no-pi-hole) I can now use the internet. My public IP address, according to https://whatsmyip.com, has not changed. Should it?
Update to the update: while I had internet access Pihole wasn’t actually working. I tried some things from that article linked above but things broke even further so I have reverted.
Dang, I was hoping that was going to work! Give me some time to take a look into this. I am trying to achieve a similar thing but ran into similar issues as you.
I’ll keep you posted if I find anything and please do the same if you figured it out 
1 Like
Hey @Capt_Barnacles,
I finally had some free time to look into this and I was able to get it up and running with Docker.
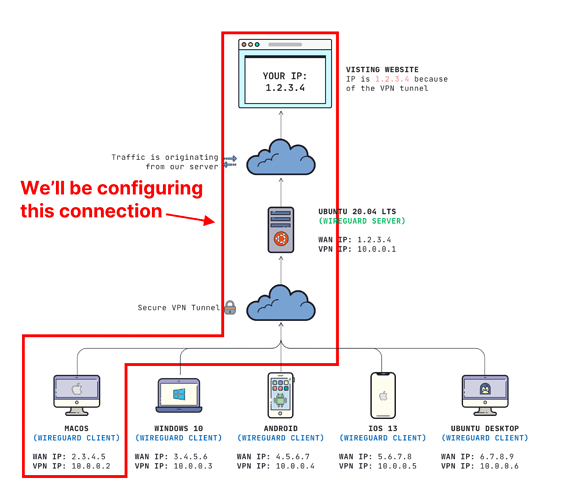
To show you how I did this, let’s assume I am configuring this Mac client…
On your Server
- Install docker
- Install piHole with Docker
This is the command that I ran. Replace your IPs with what match your network. Reference the IP addresses in the image for what addresses I used. You can also change the /var/docker-volumes path where you want to store your piHole files:
docker run -d \
--name pihole \
-p 10.0.0.1:53:53/tcp -p 10.0.0.1:53:53/udp \
-p 10.0.0.1:80:80 \
-p 10.0.0.1:443:443 \
-e TZ="UTC" \
-v "/var/docker-volumes/pihole/etc/pihole/:/etc/pihole/" \
-v "/var/docker-volumes/pihole/etc/dnsmasq.d/:/etc/dnsmasq.d/" \
--dns=127.0.0.1 --dns=1.1.1.1 \
--restart=unless-stopped \
pihole/pihole:latest
Get your password from the docker logs
You may have to wait a minute or two, but you can get your generated password by running this on your server:
docker logs pihole 2> /dev/null | grep 'password:'
Configure your client
My client config looks like this:
[Interface]
PrivateKey = abcdefghijklmnopqrstuvwxyz1234567890=+
Address = 10.0.0.3/24
DNS = 10.0.0.1
[Peer]
PublicKey = YOUR_SERVER_PUBLIC_KEY
AllowedIPs = 0.0.0.0/0
Endpoint = 1.2.3.4:51820
NOTE: Notice how my DNS is set to the Peer IP address of the server (10.0.0.1) in this case.
Use the image at the top to reference which interfaces I used.
Test it out
You should be able to connect your client and test it out by visiting a site like msn.com, yahoo.com, or any site that you have not been to in a while. You should see your queries appear in the pihole log on the dashbboard (mine is located at http://10.0.0.1/admin)
Hope this helps!
Also, instead of running the raw docker commands, you may want to use docker-compose.
You can create a docker-compose.yml file that looks like this:
version: "3"
networks:
dns:
services:
pihole:
container_name: pihole
image: pihole/pihole:latest
restart: always
volumes:
- /var/docker-volumes/pihole/etc/pihole/:/etc/pihole/
- /var/docker-volumes/pihole/etc/dnsmasq.d/:/etc/dnsmasq.d/
ports:
- "10.0.0.1:53:53/tcp"
- "10.0.0.1:53:53/udp"
- "10.0.0.1:80:80"
- "10.0.0.1:443:443"
environment:
- TZ="UTC"
- WEBPASSWORD="yourpasswordhere"
dns:
- 127.0.0.1
- 1.1.1.1
networks:
- dns
Using docker compose will make it a million times easier to run updates and migrate if needed.